Table of Contents
TCP/IP model
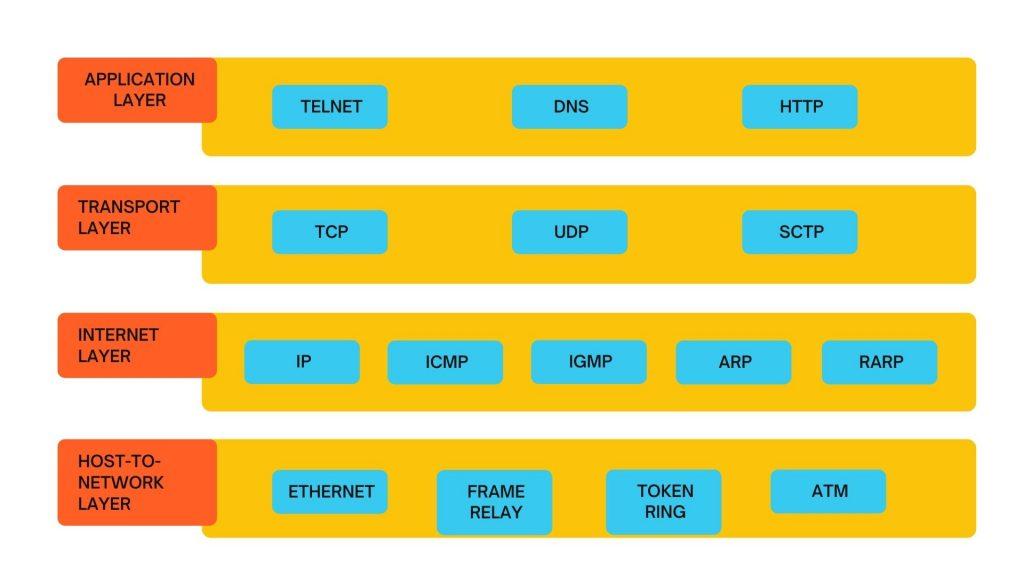
TCP/IP model was designed and developed by the Department of Defense (DoD) funded by the United States Department of Defense in the 1960s and is based on standard protocols. It stands for Transmission Control Protocol/Internet Protocol. The TCP/IP model is a concise version of the OSI model. TCP/IP model contains four layers, unlike seven layers in the OSI model. The layers are:
Host-to-Network Layer
It is the lowest layer. This layer is concerned with the physical transmission of data. TCP/IP does not specifically define any protocol here but supports all the standard protocols.
This layer is a combination of the Data Link Layer and Physical Layer of the OSI model. It looks out for hardware addressing. The protocols representing this layer allow for the physical transmission of data.
We just talked about ARP as a protocol of the Internet layer, but there is a conflict about declaring it as a protocol of Internet Layer or Network access layer. It is described as residing in layer 3, being encapsulated by layer 2 protocols.
Internet Layer
This layer defines the protocols for the logical transmission of data over the network. The main protocol in this layer is Internet Protocol (IP) and it is supported by ICMP, IGMP, RARP, and ARP.
This layer has similar functions to OSI’s Network layer. It defines the protocols for the logical transmission of data over the network. The main protocols at this layer are :
Internet Protocol (IP) – It is responsible for delivering packets from the source host to the destination host by looking at the IP addresses of packet headers. Internet Protocol has 2 versions:
IPv4 and IPv6.
IPv4 is the one that most of the websites are using currently. But IPv6 is growing in number in comparison to IPv4 addresses are limited in number when compared to the number of users.
Internet Control Message Protocol (ICMP) – It is encapsulated within IP datagrams It provides hosts with information about network problems.
Address Resolution Protocol (ARP) – It is working to find the hardware address of a host from a known IP address. ARP has several types: Reverse ARP (R-ARP), Proxy ARP (P-ARP), Gratuitous ARP (G-ARP), and Inverse ARP (I-ARP).
Transport Layer
It is responsible to deliver error-free end-to-end data. The protocols defined here are Transmission Control Protocol (TCP) and User Datagram Protocol (UDP).
This layer resembles the transport layer of the OSI model. It is responsible for end-to-end communication and error-free delivery of data. It shields the upper-layer applications from the complexities of data. The two main protocols present in this layer are :
- Transmission Control Protocol (TCP) – It is responsible to deliver error-free end-to-end data. It allows the sequencing and segmentation of data. It also has an acknowledgment feature. It controls the flow of the data through a flow control mechanism. It is a very effective protocol but increased overhead leads to increased cost.
- User Datagram Protocol (UDP) – It is the go-to protocol if your application does not require reliable transport as it is very cost-effective. Unlike TCP(connection-oriented protocol), UDP is connectionless.
Application Layer
This layer includes high-level protocols such as Telnet, DNS, HTTP, FTP, SMTP, etc. It is the top layer and defines the interface of host programs with the transport layer services.
This layer resembles the functions of the top three layers of the OSI model: Application, Presentation, and Session Layer. It is responsible for node-to-node communication and controls user-interface specifications. Some of the protocols represent in this layer are HTTP, HTTPS, FTP, TFTP, Telnet, SSH, SMTP, SNMP, NTP, DNS, DHCP, NFS, X Window, LPD.
- Hypertext transfer protocol (HTTP) – It is used by the World Wide Web to manage communications between web browsers and servers.
- HTTP-Secure (HTTPS). It is a combination of HTTP with SSL(Secure Socket Layer). It is efficient in cases where the browser needs to fill out forms, sign in, authenticate and carry out bank transactions.
- Secure Shell (SSH) – It is a terminal emulations software like Telnet. SSH is more preferable because it has the ability to maintain the encrypted connection. It sets up a secure session over a TCP/IP connection.
- Network Time Protocol(NTP) – It is used to synchronize the clocks on our computer to one standard time source. It is very useful in bank transactions.
